SAAS · CLOUD & INFRASTRUCTURE
Cloud foundations designed for safe change at scale.
We build the platform layer teams rely on when traffic, incident frequency, and compliance requirements increase. Infrastructure is code, releases are staged and reversible, identity is least-privilege, and observability is aligned to SLOs—so operations are predictable, not heroic.
THE SYSTEM
A platform layer that makes change safe and repeatable.
Infrastructure isn’t a set of tickets—it’s the delivery system for everything you ship. We treat cloud foundations as a product: environments are reproducible, releases are staged, and access is controlled by default.
The output is a platform that’s easier to operate under pressure: observability maps to SLOs, incidents become diagnosable, and compliance requirements are supported without slowing delivery.
EXECUTION DISCIPLINE
Safe releases are engineered into the pipeline.
We build cloud foundations with parity, least privilege, and SLO-driven telemetry—so teams scale without operational heroics.
01
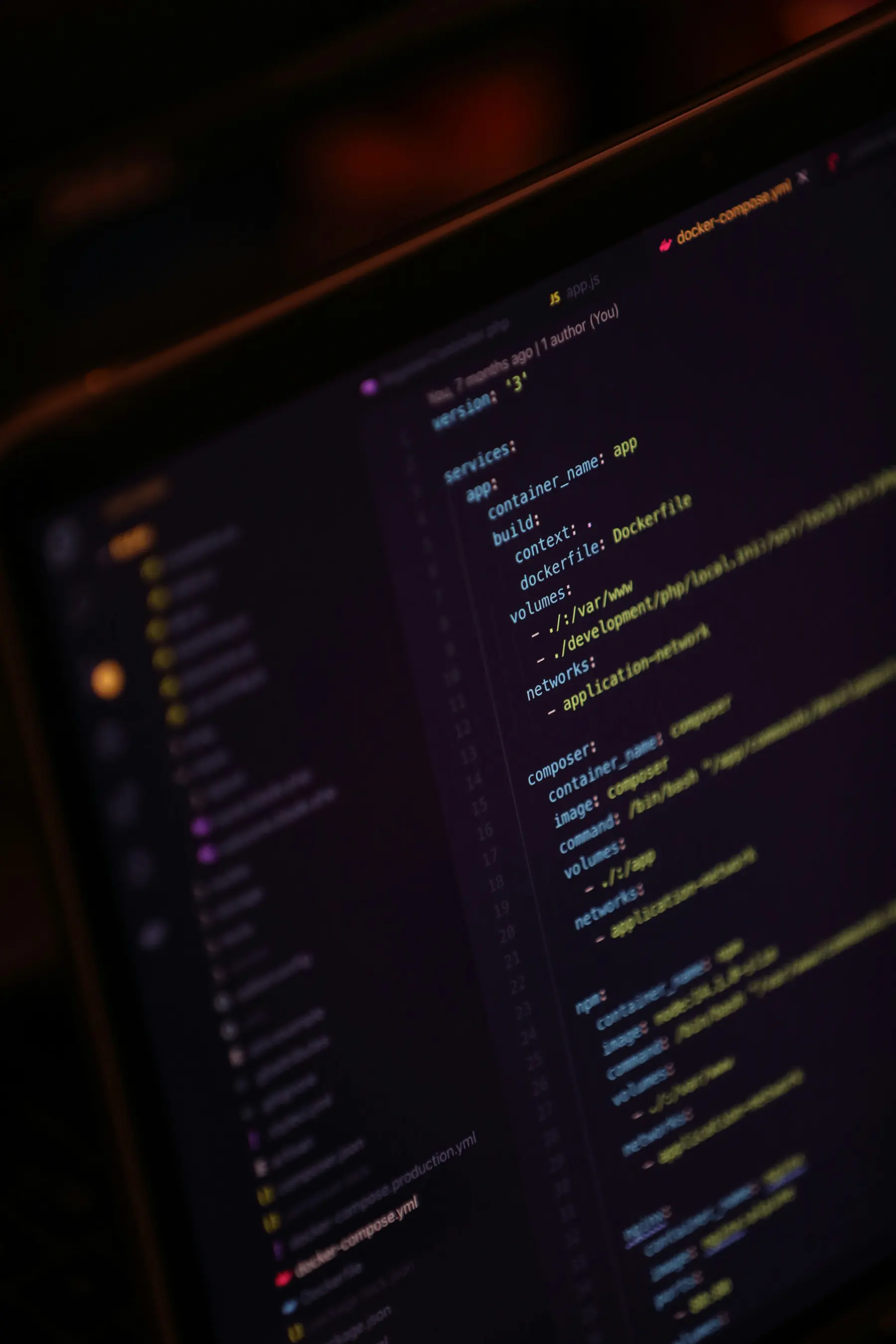
Environment parity via IaC
We define infrastructure as code so dev/staging/prod behave consistently and changes are reviewable.
- Environments are reproducible and drift is detectable.
- Changes are peer-reviewed with clear blast-radius awareness.
- Configuration is centralized and versioned.
02
Release safety
We design staged rollouts (canary/blue-green) with verification gates and automated rollback triggers.
- Deployments are observable with clear success criteria.
- Rollback paths are explicit and tested—not improvised.
- Verification includes dependency checks and smoke tests.
03
Security + compliance guardrails
We implement least privilege, secrets hygiene, and auditable change control so security scales with the platform.
- Identity is scoped, short-lived where possible, and auditable.
- Secrets are managed and rotated with policy, not habit.
- Network boundaries are explicit with clear ingress/egress controls.
ARTIFACTS & OUTCOMES
A cloud platform your team can operate with confidence.
You get IaC baselines, CI/CD pipelines, SLO dashboards, and runbooks that convert infrastructure into a controlled release system—not a manual craft.
Infrastructure-as-code baseline
Reviewable IaC for environments, networking, secrets, and compute—designed for parity and stability.
CI/CD release system
Pipelines with verification, gated rollouts, and rollback mechanisms that keep deployments safe.
Secure defaults and guardrails
IAM, network boundaries, secret management, and audit logging designed for enterprise constraints.
Observability pack
Dashboards, alerts, and tracing patterns aligned to SLOs and user impact.
Multi-tenant or environment strategy
Tenant isolation patterns, data boundaries, and operational controls for SaaS growth.
Operations handoff kit
Runbooks, on-call playbooks, and escalation paths so operation is predictable post-launch.
OPERATING QUESTIONS
The questions that define reliability and compliance posture.
We align on release strategy, access control, tenancy boundaries, observability targets, and incident readiness—before the platform is stressed by growth.
EXPLORE MORE
Other services
Adjacent capabilities that often ship alongside this service.